We previously talked about the 3 most common cyberattacks in this new era of hybrid working. Now lets hone in on phishing attacks specifically.
Leaders have been trying to tackle this issue for a long time and now with remote work, we are faced with it even more. In 2021, 83% of organisations had experiences phishing attacked and it is said that in 2022 and additional 6 billion attacked will occur with the average costs of remediating these breaches sitting at $4.65 million.
Those are some huge numbers and still on the rise.
How can leaders put more emphasis in this space? How can leaders strengthen their security posture when identifying the gaps?
Here we’ll talk a little about what a phishing email is, what it looks like, how to report it and what organisations can do to mitigate and protect any future breaches.
What is a phishing email?
A phishing scam is an email that seems legitimate but is an attempt to get your personal information, company data or steal your money.
Scammers are becoming more sophisticated with their attacks every day, it is important that you are able to identify these threats.
So what should I be looking for?
Keep an eye out for the following when you’ve received an email.
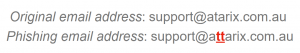
- The ‘From’ line: The first thing to pay attention to is the address you are receiving the email from. They often appear like a trusted client or colleague but when you look closely there is a subtle difference. An example would be:
- Hyperlinks: Always be cautious of clicking on embedded links unless you are sure it is from a trusted website. If the URL does not match what the text says, it’s not a good idea to click on the hyperlink.
- Company Branding: If the email looks like it’s coming from Microsoft and is asking for your credentials, look out for your company branding and logo on the sign-in and check the URL.

- Urgency: Phishing attempts will usually try to trick you with scare tactics or requests for immediate action. If the subject line or content sounds suspicious or out of character, validate with the source before taking action. Give the sender a call to confirm the request.
What do I do if I think I’ve have received one?
Use the Report Message function in Outlook to report it. That will send those looking after your tenancy or environment and Microsoft a copy to investigate.
- If you receive it in your Junk folder, you can either safely ignore it (Junk emails clear themselves after 30 days) or simply go ahead and delete it.
The key here is DO NOT OPEN THE EMAIL if it at all looks dodgy!
As a business, what measures can I put in place?
There are a few things that can be done to mitigate against any breaches:
- Adopt a security framework – adopting a security model or framework such as the Zero Trust Model is a great place to start when looking to protect your environment from all angles of attack.
- Secure your identities – apply multifactor authentication to all indentities and devices.
- Secure your passwords – ensure that all user have strong passwords and use a secure password manager.
- Training your employees – Security and phishing awareness training is a great way to stop the likelihood of each user being targeted, allowing attackers access to your environment.
Security is a key focus for us at Atarix which is why we build this into our Baseline. We strive to ensure we are always keeping you protected against the latest security threats.
If you’re looking for assistance in this space, please reach out to speak to an expert.



